Products You May Like
Since the first edition of The Ultimate SaaS Security Posture Management (SSPM) Checklist was released three years ago, the corporate SaaS sprawl has been growing at a double-digit pace. In large enterprises, the number of SaaS applications in use today is in the hundreds, spread across departmental stacks, complicating the job of security teams to protect organizations against evolving threats.
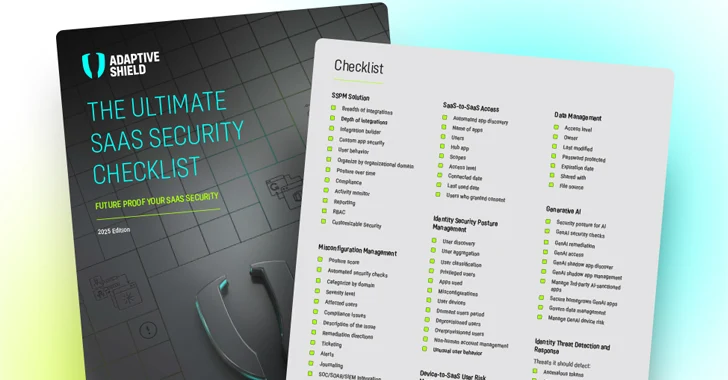
As SaaS security becomes a top priority, enterprises are turning to SaaS Security Posture Management (SSPM) as an enabler. The 2025 Ultimate SaaS Security Checklist, designed to help organizations choose an SSPM, covers all the features and capabilities that should be included in these solutions.
Before diving into each attack surface, when implementing an SSPM solution, it’s essential to cover a breadth of integrations, including out-of-the-box and custom app integrations, as well as in-depth security checks. While there are apps that are more sensitive and complex to secure, a breach can come from any app, therefore coverage is key.
Threat Prevention Essentials to Secure the SaaS Stack
The essential prevention capabilities of an SSPM to secure the entire SaaS stack should cover the following:
Misconfiguration Management
Serving as the core of an SSPM, misconfiguration management should provide deep visibility and control of all security settings across all SaaS apps for all users. It should have wide functionalities such as posture score, automated security checks, severity measurement, compliance checks, alerting, in addition to SOAR/SIEM and any ticketing system integration to fix misconfigurations using existing security tools. Such platforms should include detailed remediation plans and a robust app owner-security team collaboration infrastructure to ensure the remediation loop is properly closed.
Identity Security
Strong Identity Security Posture Management (ISPM) capabilities are of paramount importance in securing the SaaS stack. In regards to human identities, an organization needs to have the ability to govern overprivileged users, dormant users, joiners, movers, leavers, and external users, and trim permissions accordingly. This also includes enforcement of identity-centric configurations such as MFA and SSO, especially for those who have sensitive roles or access.
As users install apps, with or without the knowledge and consent of the security team, an SSPM should have the ability to monitor the non-human identities associated with connecting 3rd party apps to core hubs to mitigate risk. A SaaS security tool should have automated app discovery and management to enable security teams to see all sanctioned and shadow apps, scopes and permissions, and remediate accordingly.
Permissions Management
Getting SaaS entitlements all in one place enhances identity security posture management to reduce the attack surface and improve compliance efforts.
Sophisticated applications, such as Salesforce, Microsoft 365, Workday, Google Workspace, ServiceNow, Zendesk, and more have very complex permission structures, with layers of permissions, profiles, and permission sets. Unified visibility for the discovery of complex permissions enables security teams to better understand risk coming from any user.
Device-to-SaaS Relationship
When selecting an SSPM, make sure that it integrates with the Unified Endpoint Management system, to ensure you manage risks from your SaaS user devices. Through such a feature, the security team has insights into SaaS-user unmanaged, low-hygiene and vulnerable devices that can be susceptible to data theft.
GenAI Security Posture
SaaS providers are racing to add generative AI capabilities into SaaS applications to capitalize on the wave of productivity offered by this new form of AI. Add-ons such as Salesforce Einstein Copilot and Microsoft Copilot use GenAI to create reports, write proposals, and email customers. The ease of using GenAI tools has increased the risk of data leakage, expanded the attack surface, and opened new areas for exploitation.
When evaluating a SaaS security solution, make sure it includes GenAI monitoring, including:
- Security posture for AI apps to identify AI-driven applications with heightened risk levels
- Checks of all GenAI configurations and remediation of GenAI configuration drifts
- GenAI access to monitor user access to GenAI tools based on roles
- GenAI shadow app discovery to identify shadow apps using GenAI, including malicious apps
- Data management governance to control which data is accessible by GenAI tools
Securing Company Data to Prevent Leakage
SaaS applications contain sensitive information that could cause considerable harm to the company if made public. Additionally, many SaaS users share files from their SaaS applications with external users, such as contractors or agencies, as part of their operational process.
Security teams need visibility into the shared settings of documents that are publicly available or externally shared. This visibility enables them to close gaps in document security and prevent data leaks from occurring. An SPPM should be able to pinpoint documents, files, repositories, and other assets that are publicly available or shared with external users.
A SaaS security solution should include capabilities in the area of data leakage protection such as:
- Access level that displays whether an item is externally or publicly shared.
- A list of “shared with” users who have been granted access to the document.
- Expiration date: Shows whether the link will expire automatically and no longer be accessible by the public:
Download the full 2025 SaaS security checklist edition.
Threat Detection & Response
Identity Threat Detection and Response (ITDR) provides a second layer of protection to the SaaS stack that serves as a critical piece of the identity fabric.
When threat actors breach an application, ITDR detects and responds to identity-related threats based on detecting key Indicators of Compromise (IOCs) and User and Entity Behavior Analytics (UEBA). This triggers an alert and sets the incident response mechanism in motion.
An SSPM should include ITDR capabilities that are based on logs coming from the entire SaaS stack, this is another reason why stack coverage is so important. By extending the rich data collected across the SaaS stack, ITDR capabilities have a far richer understanding of standard user behavior and the detection of anomalies in the most accurate way.
Sample Indicators of Compromise include:
- Anomalous tokens: Identify unusual tokens, such as an access token with an extremely long validity period or a token that is passed from an unusual location
- Anomalous behavior: User acts differently than usual, such as uncharacteristically downloading high volumes of data
- Failed login spike: Multiple login failures using different user accounts from the same IP address
- Geographic behavior detection: A user logs in from two locations within a short timeframe
- Malicious SaaS applications: Installation of a third-party malicious SaaS application
- Password spray: User logs in using password spray to access a SaaS application
Choosing the Right SSPM
By developing best practices for SaaS security, organizations can grow safely with SaaS applications. To compare and choose the right SSPM for your organization, check out the full 2025 checklist edition outlining what capabilities to look for to elevate your SaaS security and be prepared to head off new challenges.
Get the complete guide along with the printable checklist here.