Products You May Like
Organizations have been worrying about cyber security since the advent of the technological age. Today, digital transformation coupled with the rise of remote work has made the need for security awareness all the more critical.
Cyber security professionals are continuously thinking about how to prevent cyber security breaches from happening, with employees and contractors often proving to be the most significant risk factor for causing cyber security incidents. Proactive cyber security professionals will find that an effective security awareness training program can significantly reduce their risk of getting exposed to a cyber incident.
For a security awareness training program to be successful, it must be measurable and yield positive, actionable results over time.
The following looks at what good security awareness looks like and how vital phishing simulations and awareness training is in devising effective cyber security programs.
The essentials of a cyber security awareness training program
Employees represent security risks mainly because they are unaware of how their actions and decisions cause security incidents. To address this cause, enterprises undertake extensive security awareness training efforts to help employees know what they should and shouldn’t do when working digitally.
The mere act of exposing employees to security training is not enough; a program is not effective unless it produces results in building real skills that change employee behavior and empower them to make the right choice in the face of a cyberattack.
To achieve this, companies must select a security awareness training that is data-driven, adaptive per employee location, takes into account role and behavior towards cyber training, is continuous and high-frequency, and engages each employee at least once a month.
Some of the key features organizations should be looking for in a security awareness program can be divided into the following.
Continuous cyber education training and a hands-on approach
The more employees are exposed to real-life phishing emails and other security risks, the more likely they are to succeed in protecting the organization and assets against phishing, malware, and many other threats. However, with cybersecurity awareness, theoretical knowledge becomes even more valuable when put into practice. Therefore training must become a hands-on learning experience with simulations and concrete action.
Identify weakest links and employ real-time feedback
Statistically, fewer than 20 percent of employees in an organization are responsible for most human error-induced mistakes. To make sure all employees are properly trained, organizations must run simulations frequently – at least once a month. This is also where continuous feedback loops come into play. By engaging or disengaging with the content, employees reflect on the security gap that exists between them and the organizational risk, illustrating the need for cybersecurity awareness training in the first place. Moreover, when security events include real-time feedback, employees immediately understand the missteps and how to prevent similar situations in the future.
Culture and the scientific training method
Cyber security awareness must be ingrained in the organization’s daily practices without feeling like a daily grind. Organizations should make training an engaging, effortless, and seamless part of employees’ daily routines, regularly encouraging continuous learning via small digestible security awareness learning bites.
Behind effective cyber security training is often a scientific method. A next gen approach to security awareness training should focus bringing together learning expertise, data science, and automation.
How to Measure Progress
Having a training program in place is a great start, but organizations must ask themselves: how do I know if my security awareness training is working?
Organizations usually rely solely at click rates (e.g. how many employees click on phishing simulations) to measure success. And this is precisely where they go wrong.
Companies must focus on progress over time, and not just measure participation.
When measuring the success of a security awareness program, it’s all about context.
Companies should look for qualitative, not simply quantitative results. For instance, if a company sends out three phishing simulations over a year, there is no way of knowing whether one was sent while an employee was on vacation or if an employee clicked because they were new to the company or whether the email went unnoticed due to a flurry of meetings and other tasks.
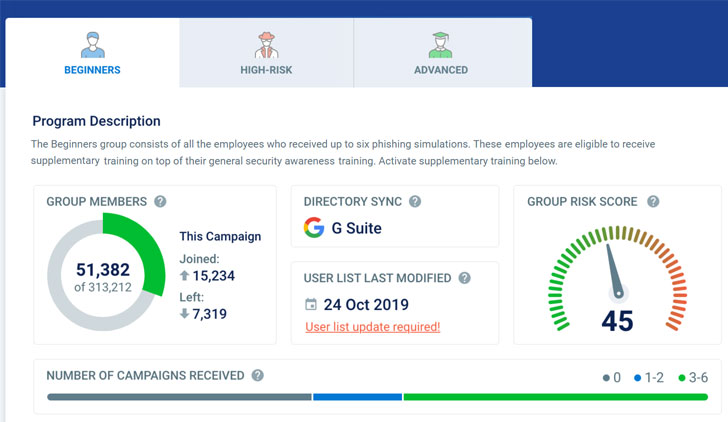 |
| Image credit: CybeReady |
When progress is measured instead of participation, teams get a clear view of the benefits of a security awareness training solution over time. Instead of looking at the company as one block of employees, it would be worthwhile to approach them individually with specific strengths and weaknesses. To evaluate the impact of your security awareness training, you need actionable data to identify valuable metrics such as:
- High-risk employees: The number of employees who fail to learn at a good pace and avoid more scams over time.
- Resilience: The level of security awareness in the company or even within specific teams.
- Meantime between failures: Proving that employee learning is occurring and that retention is improving over time. In machinery, MTBF is used to measure the amount of time since the machine failed last. In the security awareness industry, MTBF shows the resilience of an organization. If employees have fewer simulation failures and mistakes are decreasing, the employees are acquiring knowledge from the program, and best of all – retaining it.
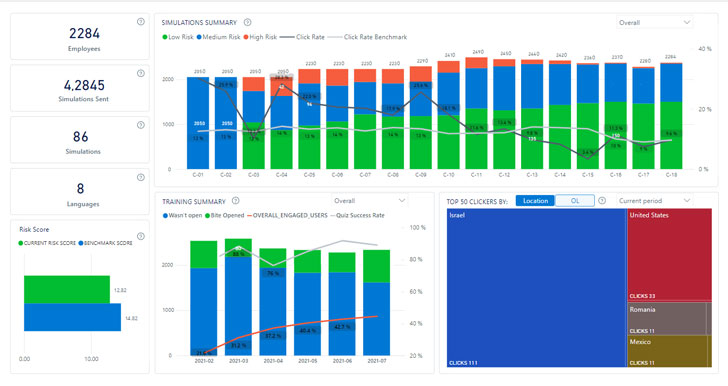 |
| Image credit: CybeReady |
An effective security awareness program requires the right platform
Security professionals who wish to address security risks in their organizations need to ensure that their employees know daily security risks. An ongoing, employee-centric, and engaging security awareness program is one of the best ways to have vigilant employees.
Organizations must foster security awareness to build a culture of readiness to mitigate security risks effectively. CybeReady addresses this by offering a fully autonomous, data-driven security readiness platform that delivers, measures, and optimizes complete out-of-the-box awareness training that is continuous, contextual, and adaptive.
 |
| Image credit: CybeReady |
CybeReady’s Security Awareness Training platform offers key capabilities :
- Training and simulation content is adapted based on employee role and locale
- Training and simulation content and frequency auto-adapt to mitigate measured risks
- No IT effort required
- One-click executive reporting
- Measurements provide progress improvements metrics
- Proven results :
200% higher employee engagement
400% increase in Employee Resilience Score (within 12 months)
80% reduction in high-risk group size
Final thoughts
Despite the broad adoption of first-generation security awareness solutions, the human element continues to be a primary catalyst for data breaches, with phishing accounting for 36% of breaches. This means that organizations need to turn security awareness into a readiness culture to mitigate security risks effectively.
CybeReady empowers enterprises with a comprehensive human-centric security awareness training program that is easy to deploy, operate and measure.
Get started with a cybersecurity training program that really works
