Products You May Like
The cryptojacking group known as Kinsing has demonstrated its ability to continuously evolve and adapt, proving to be a persistent threat by swiftly integrating newly disclosed vulnerabilities to exploit arsenal and expand its botnet.
The findings come from cloud security firm Aqua, which described the threat actor as actively orchestrating illicit cryptocurrency mining campaigns since 2019.
Kinsing (aka H2Miner), a name given to both the malware and the adversary behind it, has consistently expanded its toolkit with new exploits to enroll infected systems in a crypto-mining botnet. It was first documented by TrustedSec in January 2020.
In recent years, campaigns involving the Golang-based malware have weaponized various flaws in Apache ActiveMQ, Apache Log4j, Apache NiFi, Atlassian Confluence, Citrix, Liferay Portal, Linux, Openfire, Oracle WebLogic Server, and SaltStack to breach vulnerable systems.
Other methods have also involved exploited misconfigured Docker, PostgreSQL, and Redis instances to obtain initial access, after which the endpoints are marshaled into a botnet for crypto-mining, but not before disabling security services and removing rival miners already installed on the hosts.
Subsequent analysis by CyberArk in 2021 unearthed commonalities between Kinsing and another malware called NSPPS, concluding that both the strains “represent the same family.”
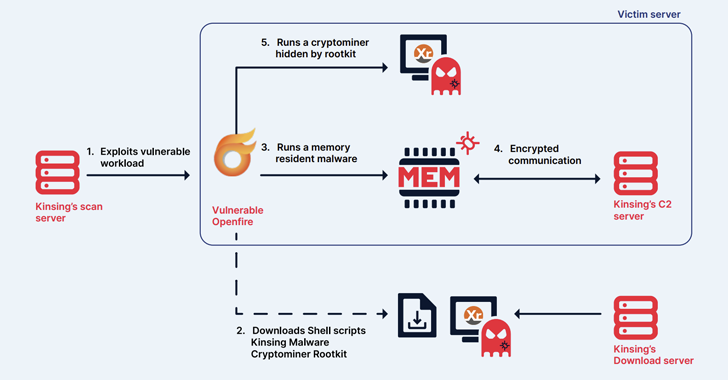
Kinsing’s attack infrastructure falls into three primary categories: Initial servers used for scanning and exploiting vulnerabilities, download servers responsible for staging payloads and scripts, and command-and-control (C2) servers that maintain contact with compromised servers.
The IP addresses used for C2 servers resolve to Russia, while those that are used to download the scripts and binaries span countries like Luxembourg, Russia, the Netherlands, and Ukraine.
“Kinsing targets various operating systems with different tools,” Aqua said. “For instance, Kinsing often uses shell and Bash scripts to exploit Linux servers.”
“We’ve also seen that Kinsing is targeting Openfire on Windows servers using a PowerShell script. When running on Unix, it’s usually looking to download a binary that runs on x86 or ARM.”
Another notable aspect of the threat actor’s campaigns is that 91% of the targeted applications are open-source, with the group mainly singling runtime applications (67%), databases (9%), and cloud infrastructure (8).
 |
| Credit: Forescout |
An extensive analysis of the artifacts has further revealed three distinct categories of programs –
- Type I and Type II scripts, which are deployed post initial access and are used to download next-stage attack components, eliminate competition, and evade defenses by disabling firewall, terminating security tools like SELinux, AppArmor, and Aliyun Aegis, and deploying a rootkit to hide the malicious processes
- Auxiliary scripts, which are designed to accomplish initial access by exploiting a vulnerability, disable specific security components associated with Alibaba Cloud and Tencent Cloud services from a Linux system, open a reverse shell to a server under the attacker’s control, and facilitate the retrieval of miner payloads
- Binaries, which act as a second-stage payload, including the core Kinsing malware and the crypto-miner to miner Monero
The malware, for its part, is engineered to keep tabs on the mining process and share its process identifier (PID) with the C2 server, perform connectivity checks, and send execution results, among others.
“Kinsing targets Linux and Windows systems, often by exploiting vulnerabilities in web applications or misconfigurations such as Docker API and Kubernetes to run cryptominers,” Aqua said. “To prevent potential threats like Kinsing, proactive measures such as hardening workloads pre-deployment are crucial.”
The disclosure comes as botnet malware families are increasingly finding ways to broaden their reach and recruit machines into a network for carrying out malicious activities.
This is best exemplified by P2PInfect, a Rust malware that has been found to exploit poorly-secured Redis servers to deliver variants compiled for MIPS and ARM architectures.
“The main payload is capable of performing various operations, including propagating and delivering other modules with filenames that speak for themselves like miner and winminer,” Nozomi Networks, which discovered samples targeting ARM earlier this year, said.
“As its name suggests, the malware is capable of performing Peer-to-Peer (P2P) communications without relying on a single Command and Control server (C&C) to propagate attackers’ commands.”