Products You May Like
Phishing campaigns delivering malware families such as DarkGate and PikaBot are following the same tactics previously used in attacks leveraging the now-defunct QakBot trojan.
“These include hijacked email threads as the initial infection, URLs with unique patterns that limit user access, and an infection chain nearly identical to what we have seen with QakBot delivery,” Cofense said in a report shared with The Hacker News.
“The malware families used also follow suit to what we would expect QakBot affiliates to use.”
QakBot, also called QBot and Pinkslipbot, was shut down as part of a coordinated law enforcement effort codenamed Operation Duck Hunt earlier this August.
The use of DarkGate and PikaBot in these campaigns is not surprising as they can both act as conduits to deliver additional payloads to compromised hosts, making them both an attractive option for cybercriminals.
PikaBot’s parallels to QakBot were previously highlighted by Zscaler in its analysis of the malware in May 2023, noting similarities in the “distribution methods, campaigns, and malware behaviors.”
DarkGate, for its part, incorporates advanced techniques to evade detection by antivirus systems, alongside capabilities to log keystrokes, execute PowerShell, and implement a reverse shell that allows its operators to commandeer an infected host remotely.
“The connection is bidirectional, meaning the attackers can send commands and receive responses in real-time, enabling them to navigate the victim’s system, exfiltrate data, or perform other malicious actions,” Sekoia said in a new technical report of the malware.
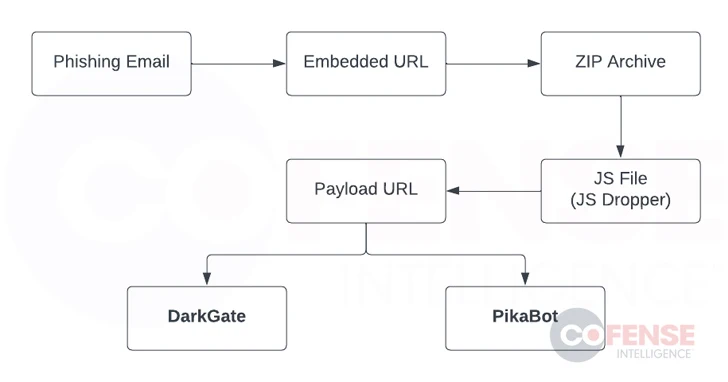
Cofense’s analysis of the high-volume phishing campaign shows that it targets a wide range of sectors, with the attack chains propagating a booby-trapped URL pointing to a ZIP archive in hijacked email threads.
The ZIP archive contains a JavaScript dropper that, in turn, contacts a second URL to download and run either the DarkGate or PikaBot malware.
A noteworthy variant of the attacks has been observed taking advantage of Excel add-in (XLL) files in lieu of JavaScript droppers to deliver the final payloads.
“A successful DarkGate or PikaBot infection could lead to the delivery of advanced crypto mining software, reconnaissance tools, ransomware, or any other malicious file the threat actors wish to install on a victim’s machine,” Cofense said.