Products You May Like
A new variant of an Apple macOS malware called XLoader has surfaced in the wild, masquerading its malicious features under the guise of an office productivity app called “OfficeNote.”
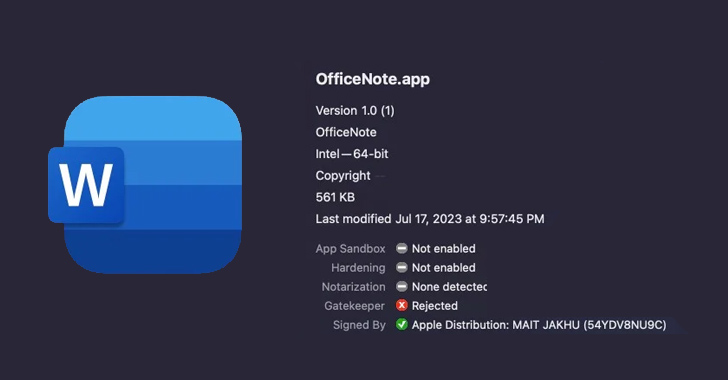
“The new version of XLoader is bundled inside a standard Apple disk image with the name OfficeNote.dmg,” SentinelOne security researchers Dinesh Devadoss and Phil Stokes said in a Monday analysis. “The application contained within is signed with the developer signature MAIT JAKHU (54YDV8NU9C).”
XLoader, first detected in 2020, is considered a successor to Formbook and is an information stealer and keylogger offered under the malware-as-a-service (MaaS) model. A macOS variant of the malware emerged in July 2021, distributed as a Java program in the form of a compiled .JAR file.

“Such files require the Java Runtime Environment, and for that reason the malicious .jar file will not execute on a macOS install out of the box, since Apple stopped shipping JRE with Macs over a decade ago,” the cybersecurity firm noted at the time.
The latest iteration of XLoader gets around this limitation by switching to programming languages such as C and Objective C, with the disk image file signed on July 17, 2023. Apple has since revoked the signature.
SentinelOne said it detected multiple submissions of the artifact on VirusTotal all through the month of July 2023, indicating a widespread campaign.
“Advertisements on crimeware forums offer the Mac version for rental at $199/month or $299/3 months,” the researchers said. “Interestingly, this is relatively expensive compared to Windows variants of XLoader, which go for $59/month and $129/3 months.”
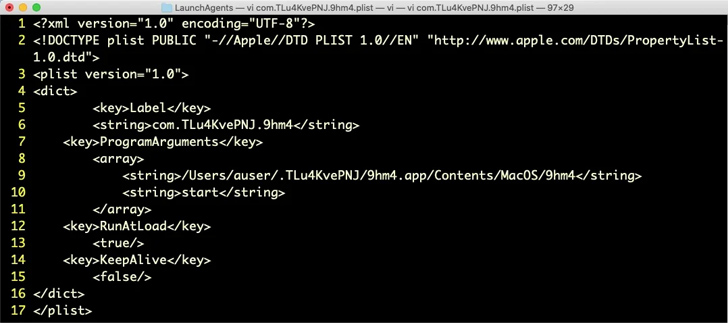
Once executed, OfficeNote throws an error message saying it “can’t be opened because the original item can’t be found,” but, in reality, it installs a Launch Agent in the background for persistence.

XLoader is designed to harvest clipboard data as well as information stored in the directories associated with web browsers such as Google Chrome and Mozilla Firefox. Safari, however, is not targeted.
Besides taking steps to evade analysis both manually and by automated solutions, the malware is configured to run sleep commands to delay its execution and avoid raising any red flags.
“XLoader continues to present a threat to macOS users and businesses,” the researchers concluded.
“This latest iteration masquerading as an office productivity application shows that the targets of interest are clearly users in a working environment. The malware attempts to steal browser and clipboard secrets that could be used or sold to other threat actors for further compromise.”