Products You May Like
A set of 38 security vulnerabilities has been uncovered in wireless industrial internet of things (IIoT) devices from four different vendors that could pose a significant attack surface for threat actors looking to exploit operational technology (OT) environments.
“Threat actors can exploit vulnerabilities in Wireless IIoT devices to gain initial access to internal OT networks,” Israeli industrial cybersecurity company Otorio said. “They can use these vulnerabilities to bypass security layers and infiltrate target networks, putting critical infrastructure at risk or interrupting manufacturing.”
The flaws, in a nutshell, offer a remote entry point for attack, enabling unauthenticated adversaries to gain a foothold and subsequently use it as leverage to spread to other hosts, thereby causing significant damage.
Some of the identified shortcomings could be chained to give an external actor direct access to thousands of internal OT networks over the internet, security researcher Roni Gavrilov said.
Of the 38 defects, three affect ETIC Telecom’s Remote Access Server (RAS) – CVE-2022-3703, CVE-2022-41607, and CVE-2022-40981 – and could be abused to completely seize control of susceptible devices.
Five other vulnerabilities concern InHand Networks InRouter 302 and InRouter 615 that, if exploited, could result in command injection, information disclosure, and code execution.
Specifically, it entails taking advantage of issues in the “Device Manager” cloud platform, which permits operators to perform remote actions like configuration changes and firmware upgrades, to compromise every cloud-managed InRouter device with root privileges.
Also identified are two weaknesses in Sierra Wireless AirLink Router (CVE-2022-46649 and CVE-2022-46650) that could allow a loss of sensitive information and remote code execution. The remaining flaws are still under responsible disclosure.
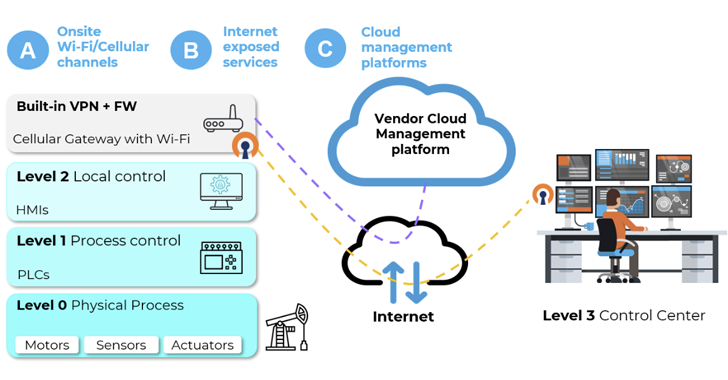
The findings underscore how OT networks could be put at risk by making IIoT devices directly accessible on the internet, effectively creating a “single point of failure” that can bypass all security protections.
Alternatively, local attackers can break into industrial Wi-Fi access points and cellular gateways by targeting on-site Wi-Fi or cellular channels, leading to adversary-in-the-middle (AitM) scenarios with adverse potential impact.
The assaults can range from targeting weak encryption schemes to coexistence attacks aimed at combo chips used widely in electronic devices.
To pull this off, threat actors can utilize platforms like WiGLE – a database of different wireless hotspots worldwide – to identify high-value industrial environments, physically locate them, and exploit the access points from close proximity, Otorio noted.
As countermeasures, it’s recommended to disable insecure encryption schemes, hide Wi-Fi network names, disable unused cloud management services, and take steps to prevent devices from being publicly accessible.
“The low complexity of exploit, combined with the broad potential impact, makes wireless IIoT devices and their cloud-based management platforms an enticing target for attackers looking to breach industrial environments,” the company said.
The development also comes as Otorio disclosed details of two high-severity flaws in Siemens Automation License Manager (CVE-2022-43513 and CVE-2022-43514) that could be combined to gain remote code execution and privilege escalation. The bugs were patched by Siemens in January 2023.