Products You May Like
Nation-state threat actors are increasingly adopting and integrating the Sliver command-and-control (C2) framework in their intrusion campaigns as a replacement for Cobalt Strike.
“Given Cobalt Strike’s popularity as an attack tool, defenses against it have also improved over time,” Microsoft security experts said. “Sliver thus presents an attractive alternative for actors looking for a lesser-known toolset with a low barrier for entry.”
Sliver, first made public in late 2019 by cybersecurity company BishopFox, is a Go-based open source C2 platform that supports user-developed extensions, custom implant generation, and other commandeering options.
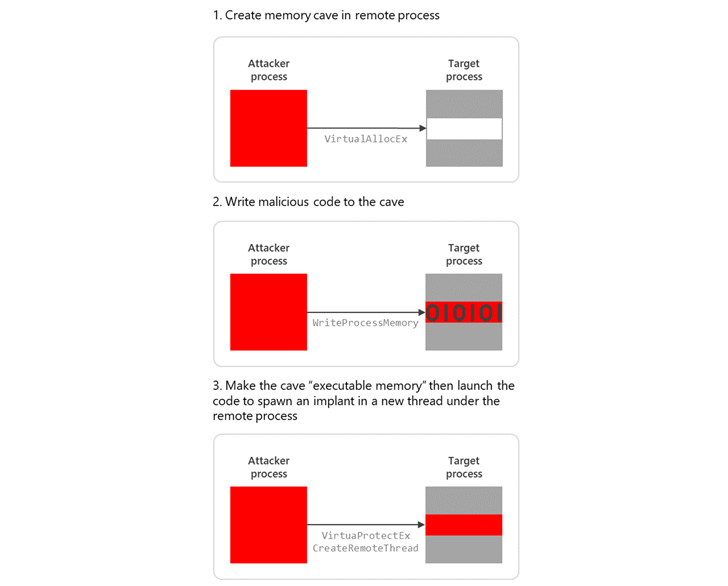
“A C2 framework usually includes a server that accepts connections from implants on a compromised system, and a client application that allows the C2 operators to interact with the implants and launch malicious commands,” Microsoft said.
Besides facilitating long-term access to infected hosts, the cross-platform kit is also known to deliver stagers, which are payloads primarily intended to retrieve and launch a fully-featured backdoor on compromised systems.
Included among its users is a prolific ransomware-as-service (RaaS) affiliate tracked as DEV-0237 (aka FIN12) that has previously leveraged initial access acquired from other groups (aka initial access brokers) to deploy various ransomware strains such as Ryuk, Conti, Hive, and BlackCat.
Microsoft said it recently observed cybercrime actors dropping Sliver and other post-exploitation software by embedding them within the Bumblebee (aka COLDTRAIN) loader, which emerged earlier this year as a successor to BazarLoader and shares links with the larger Conti syndicate.
The migration from Cobalt Strike to a freely available tool is seen as an attempt on the part of adversaries to decrease their chances of exposure in a compromised environment and render attribution challenging, giving their campaigns an increased level of stealth and persistence.
Sliver is not the only framework that has caught the attention of malicious actors. In recent months, campaigns undertaken by a suspected Russian state-sponsored group have involved another legitimate adversarial attack simulation software named Brute Ratel.
“Sliver and many other C2 frameworks are yet another example of how threat actors are continually attempting to evade automated security detections,” Microsoft said.