Products You May Like
A cyberespionage group with ties to North Korea has resurfaced with a stealthier variant of its remote access trojan called Konni to attack political institutions located in Russia and South Korea.
“The authors are constantly making code improvements,” Malwarebytes researcher Roberto Santos said. “Their efforts are aimed at breaking the typical flow recorded by sandboxes and making detection harder, especially via regular signatures as critical parts of the executable are now encrypted.”
Most recent intrusions staged by the group, believed to be operating under the Kimsuky umbrella, involved targeting the Russian Federation’s Ministry of Foreign Affairs (MID) with New Year lures to compromise Windows systems with malware.
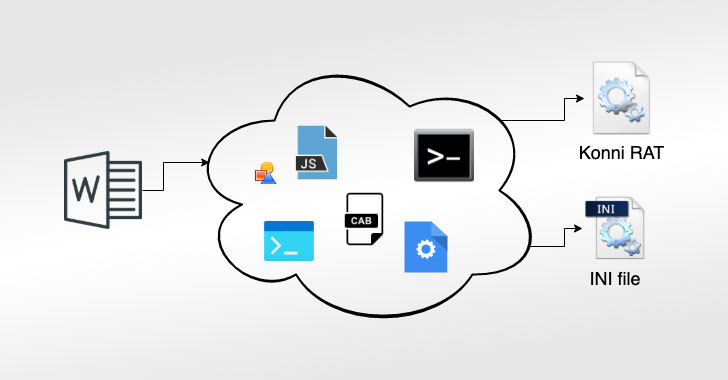
The infections, as with other attacks of this kind, starts with a malicious Microsoft Office document that, when opened, initiates a mult-stage process that involves several moving parts that help the attackers elevate privileges, evade detection, and ultimately deploy the Konni RAT payload on compromised systems.
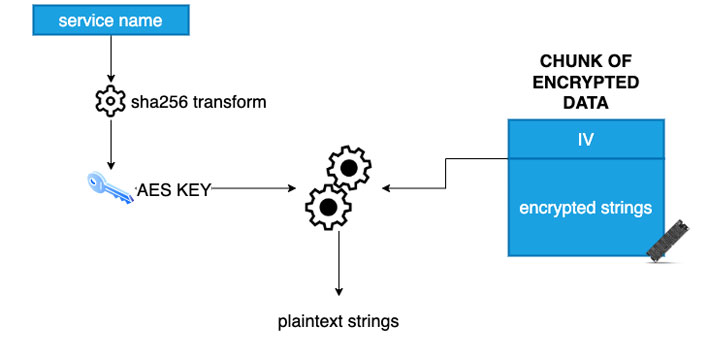
A new addition to the backdoor’s existing capabilities is the transition from Base64 encoding to AES encryption to protect its strings and for obfuscating their true purpose. On top of that, the various support files dropped to facilitate the compromise are also now encrypted using AES.
“Cleverly, they reused the algorithm used for string protection, making the file layout identical to the protected strings layout, as they appear in raw memory,” Santox detailed.
The significant updates are an example of how quickly sophisticated actors can evolve their tactics and techniques to create something potent and effective that can go past security and detection layers.